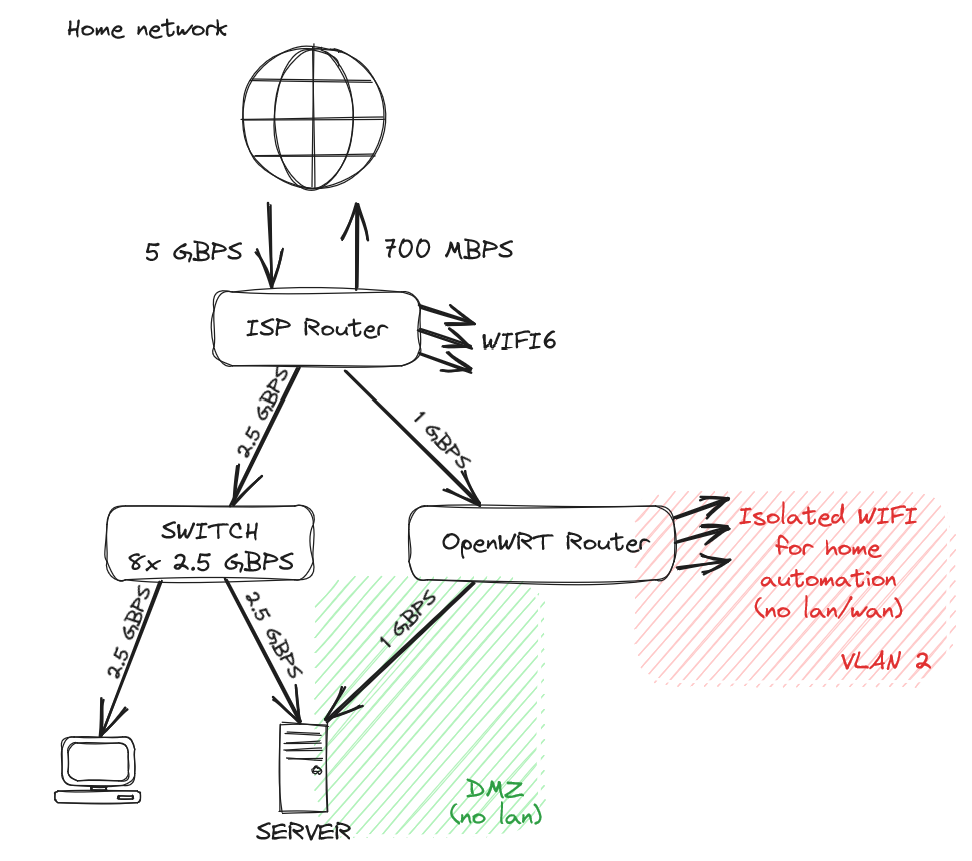
Dedicated wifi for automation allows me to have devices such as Xiaomi Vaccuum, or security camera not phoning home. OpenWRT with good firewall rules completely isolate my "public" containers/VMs from my lan.
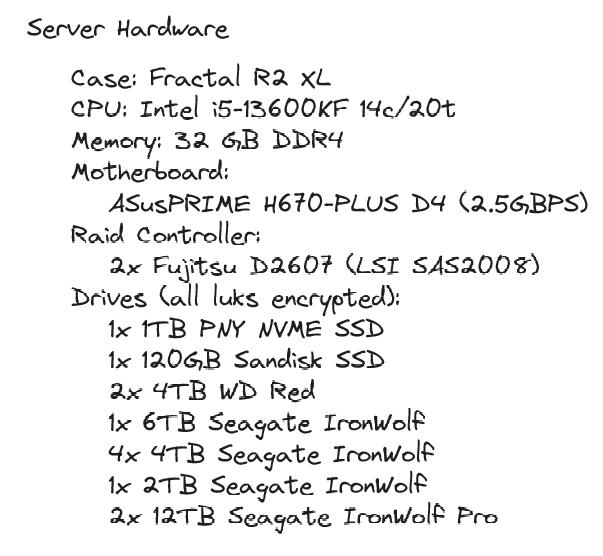
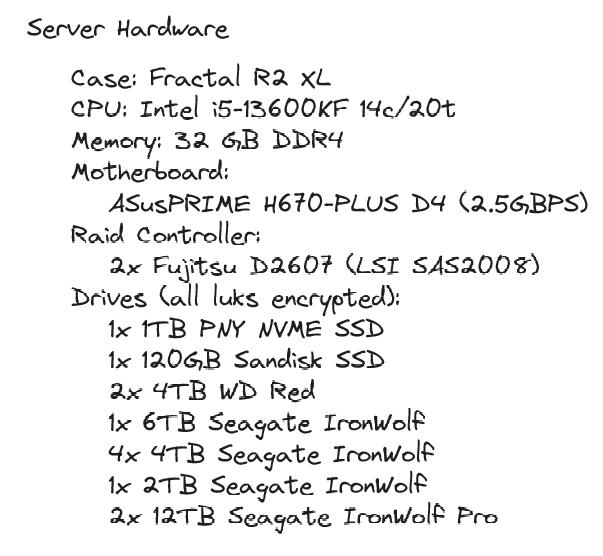
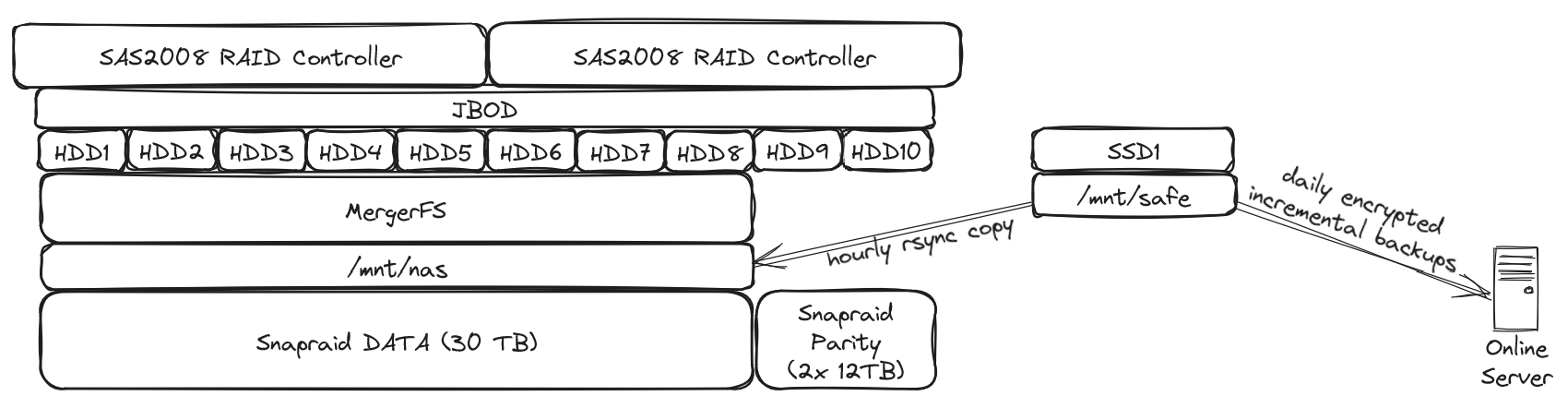
Server was built over time, disk by disk. I'm now aiming to buy only 12TB drives, but I got to sacrifice the first two as parity...
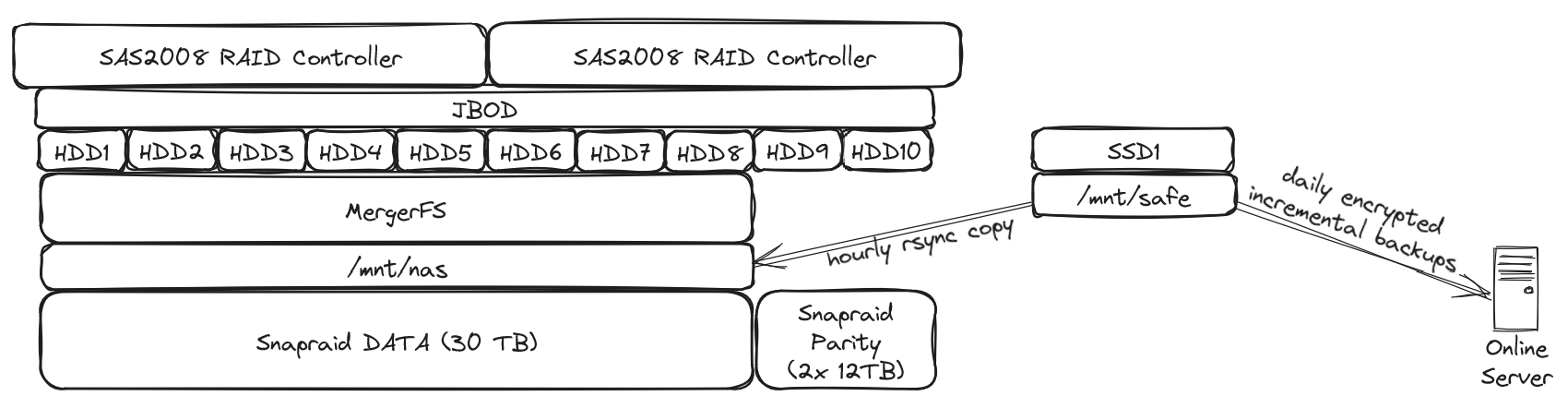
I just love the simplicity of snapraid / mergerfs. Even if I were to loose 3 disks (my setup allows me the loss of 2 disks), I'd only loose data that's on these disks, not the whole array. I lost one drive once, recovery went well and was relatively easy.
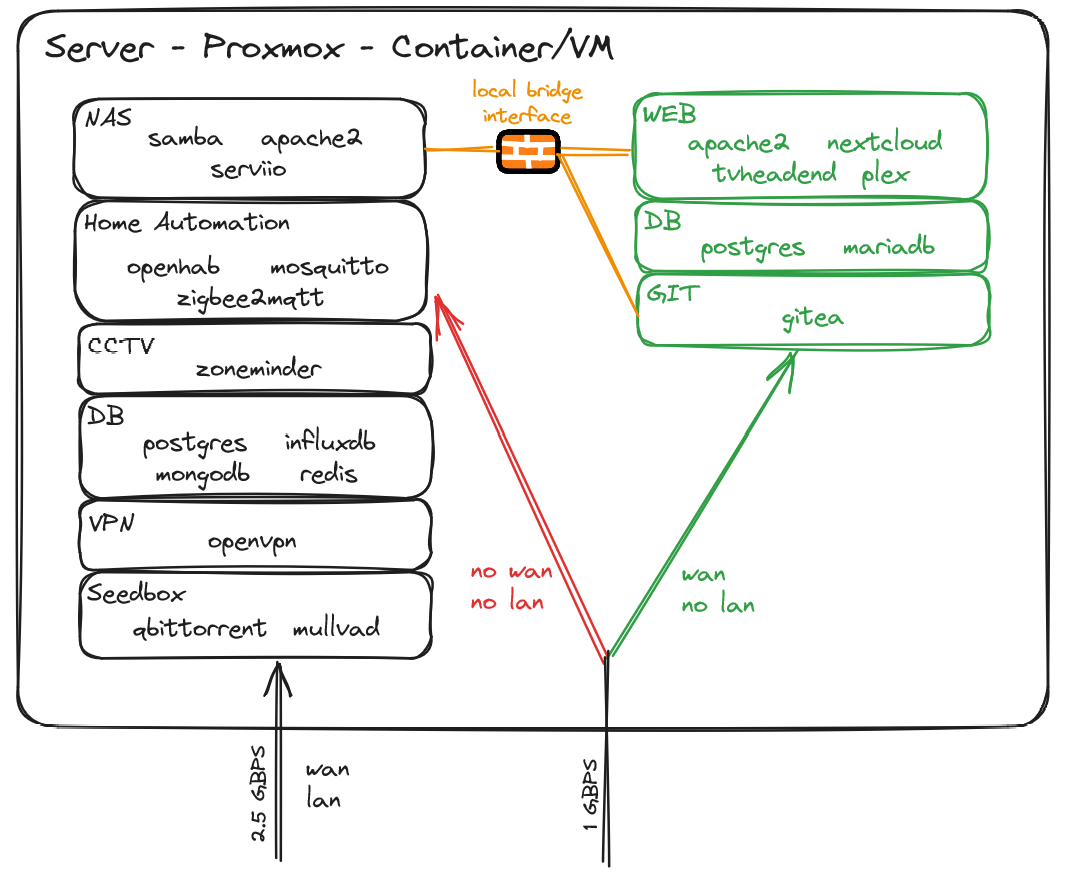
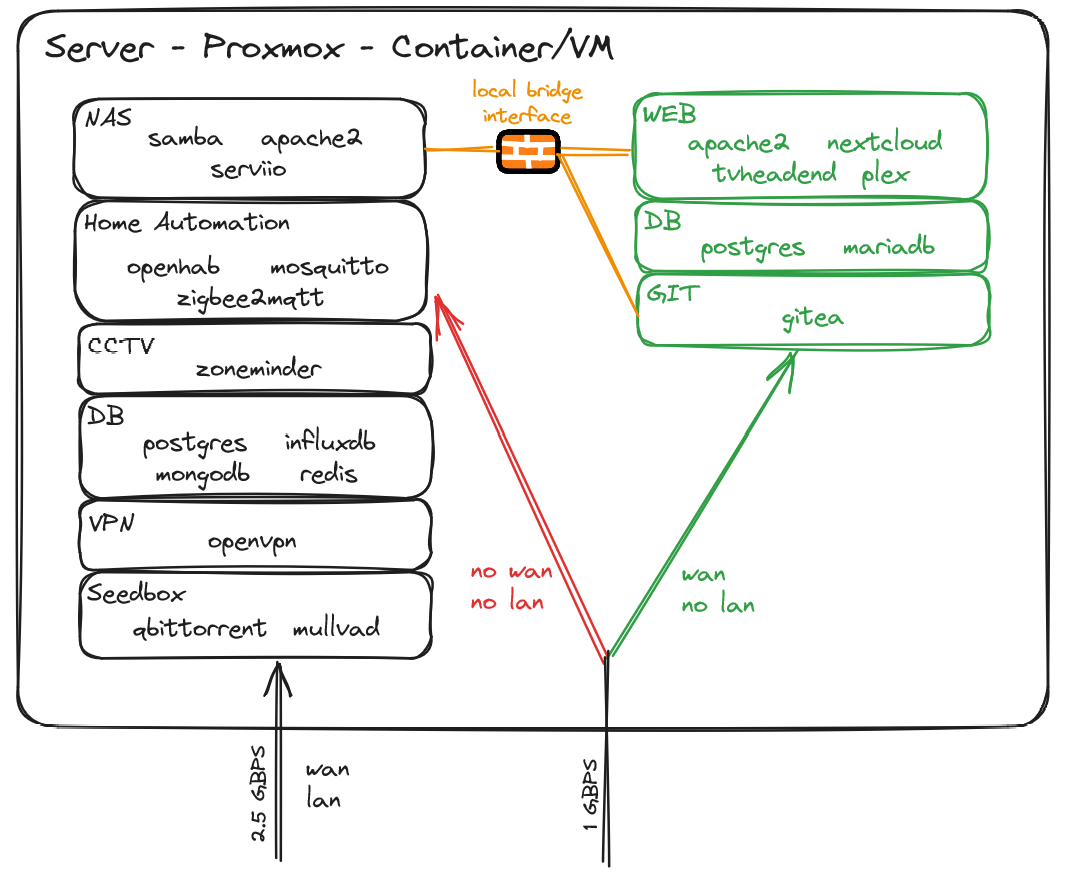
I try to keep things separated and I may be running a bit too many containers/vms, but well, I got resources to spare :)