this post was submitted on 15 Sep 2025
852 points (98.1% liked)
memes
17723 readers
3275 users here now
Community rules
1. Be civil
No trolling, bigotry or other insulting / annoying behaviour
2. No politics
This is non-politics community. For political memes please go to !politicalmemes@lemmy.world
3. No recent reposts
Check for reposts when posting a meme, you can only repost after 1 month
4. No bots
No bots without the express approval of the mods or the admins
5. No Spam/Ads/AI Slop
No advertisements or spam. This is an instance rule and the only way to live. We also consider AI slop to be spam in this community and is subject to removal.
A collection of some classic Lemmy memes for your enjoyment
Sister communities
- !tenforward@lemmy.world : Star Trek memes, chat and shitposts
- !lemmyshitpost@lemmy.world : Lemmy Shitposts, anything and everything goes.
- !linuxmemes@lemmy.world : Linux themed memes
- !comicstrips@lemmy.world : for those who love comic stories.
founded 2 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
Don't expose the website. That's the point. Only connect remotely via wireguard.
If you must expose the website, I also provided options in my original post.
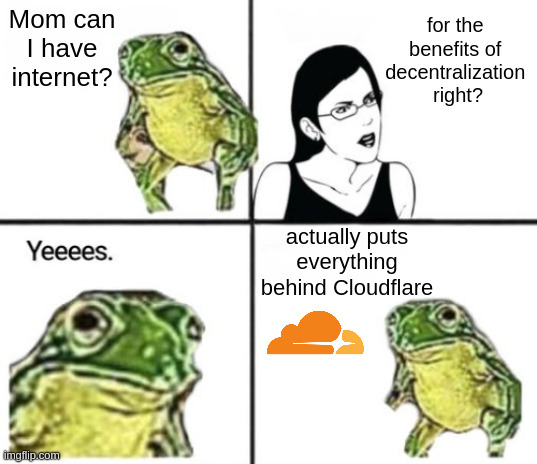
I think you misunderstood; if I run a publicly accessible website (like a Lemmy instance), those ports need to be opened.
A cheap VPS hosting
https://anubis.techaro.lol/docs/admin/installation/
as a reverse proxy may work. The VPS will do the work of verifying requests and stopping bad requests from hitting the target resource. Though certainly if the DDoS is a matter of a massive botnet raiding your domain it may not work as well as something like cloudflare
Anubis does not prevent a ddos attack and only shifts the saturation point to your VPS. Anubis is the answer for bots and ai scrappers, not DDoS.
Sure, but to someone running a website out of their house, 100,000 bots trying to hit the site at the same time to scrape it is going to have the same effect. So yes, you're correct, Anubis has nothing to do with stopping a literal DDoS attack, but it does help smaller websites stay alive by avoiding responding to requests from scrapers or one-off malicious agents.
Yes, I've addressed this in my original message.
Get yourself a 3$/month VPS, they almost all come with DDoS protection, and reverse proxy from there. Either restrict the ports on your home network to only that IP, or better yet tunnel all the traffic via Wireguard.
Obviously if you're hosting a large server this is another matter, but nevertheless almost all serious hosting services offer in house DDoS protection.
But the comment I was originally replying to specifically refered to homelabs.
What would be a good resource to, like, relearn modern networking stuff cuz some of these solutions are totally new ideas to me? I was CISCO and A+ certified way back in 2003; but the only thing I ever really used from those classes and training since then was making cables and setting up smaller, simple networks for home or small businesses. I get the sense a fuckton has changed and this exchange made me want to brush up.
A fuckton is an understatement.
I found just doing it the best for me. Start with proxmox hypervisor on some old pc. Start running a bunch of services. Some documentation mentions "heres how you set it up behind a reverse proxy". "Hmm...whats that" is pretty much how i learned it.
Then compare with people in the homelab communities who are doing differently and find out why.
There is no point in hosting a website if it's not accessible from the Web.
Again, this thread replying to the original comment is talking about homelabs.
But also, again, this is addressed in the second half of my comment.