this post was submitted on 07 Jan 2025
596 points (96.6% liked)
linuxmemes
21741 readers
1033 users here now
Hint: :q!
Sister communities:
Community rules (click to expand)
1. Follow the site-wide rules
- Instance-wide TOS: https://legal.lemmy.world/tos/
- Lemmy code of conduct: https://join-lemmy.org/docs/code_of_conduct.html
2. Be civil
- Understand the difference between a joke and an insult.
- Do not harrass or attack members of the community for any reason.
- Leave remarks of "peasantry" to the PCMR community. If you dislike an OS/service/application, attack the thing you dislike, not the individuals who use it. Some people may not have a choice.
- Bigotry will not be tolerated.
- These rules are somewhat loosened when the subject is a public figure. Still, do not attack their person or incite harrassment.
3. Post Linux-related content
- Including Unix and BSD.
- Non-Linux content is acceptable as long as it makes a reference to Linux. For example, the poorly made mockery of
sudoin Windows. - No porn. Even if you watch it on a Linux machine.
4. No recent reposts
- Everybody uses Arch btw, can't quit Vim, <loves/tolerates/hates> systemd, and wants to interject for a moment. You can stop now.
Please report posts and comments that break these rules!
Important: never execute code or follow advice that you don't understand or can't verify, especially here. The word of the day is credibility. This is a meme community -- even the most helpful comments might just be shitposts that can damage your system. Be aware, be smart, don't fork-bomb your computer.
founded 2 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
It happens, though.
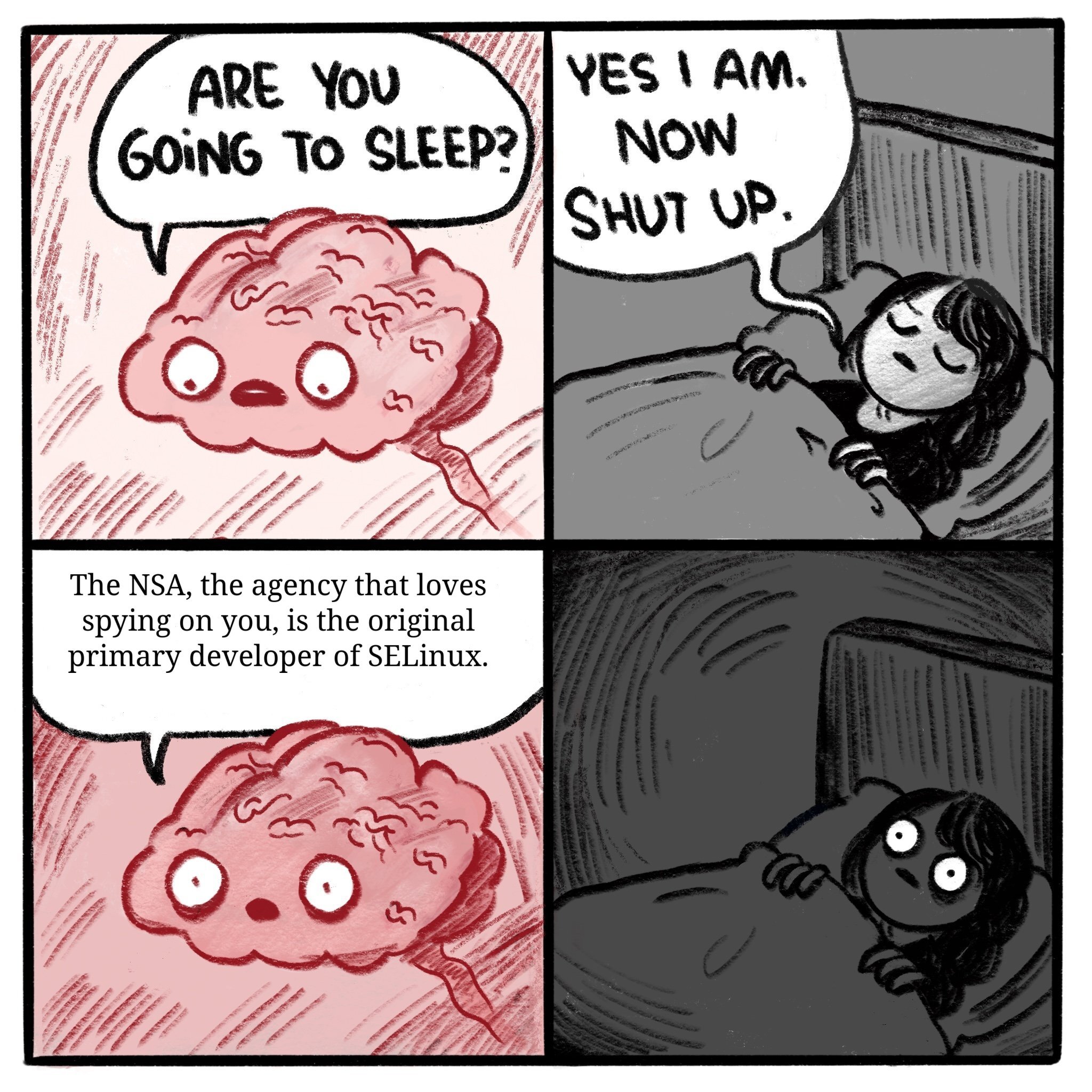
Though this implies that the Department of Defense doesn't want to use compromised tools, since DARPA is DoD. NSA is also DoD.
They wouldn't want to use or derive any compromised software themselves. They would want any adversaries to have it implemented.
People don't understand that the way a backdoor is usually implemented is not going to be obviously saying "backdoor_here", neither it will look like a some magic code loading a large string and unzipping it on the fly -- that's sus af. What you will see is some "play video" functionality that has a very subtle buffer overflow bug that's also not trivially triggerable.
This already happened with WhatsApp.
Honestly I think a lot of backdoors are just unintentionally exploits that are not disclosed
I did some follow-up research and found that subsequent audits found no backdoors. They're either incredibly sneaky, or the person making these claims wasn't being entirely honest.
Do you know of any good comprehensive followup to this? A quick search shows me lots of outdated info and inconclusive articles. Do you know if they conclusively found anything or if there is a good writeup on the whole situation?
I don't have such a source, but the Cybersecurity community throw accusations around easily, and are loathe to ever bless any software as completely innocent - which is a good thing.
When the accusations stop, the issue has either been addressed (typical outcome), or the product owner was written off by the Cybersecurity community as a lost cause (rare, but it happens).