Immich is an amazing piece of software, but because it holds such personal data I have only ever felt comfortable accessing it via VPN or mTLS. This meant that I could never share any photos, which had been really bugging me.
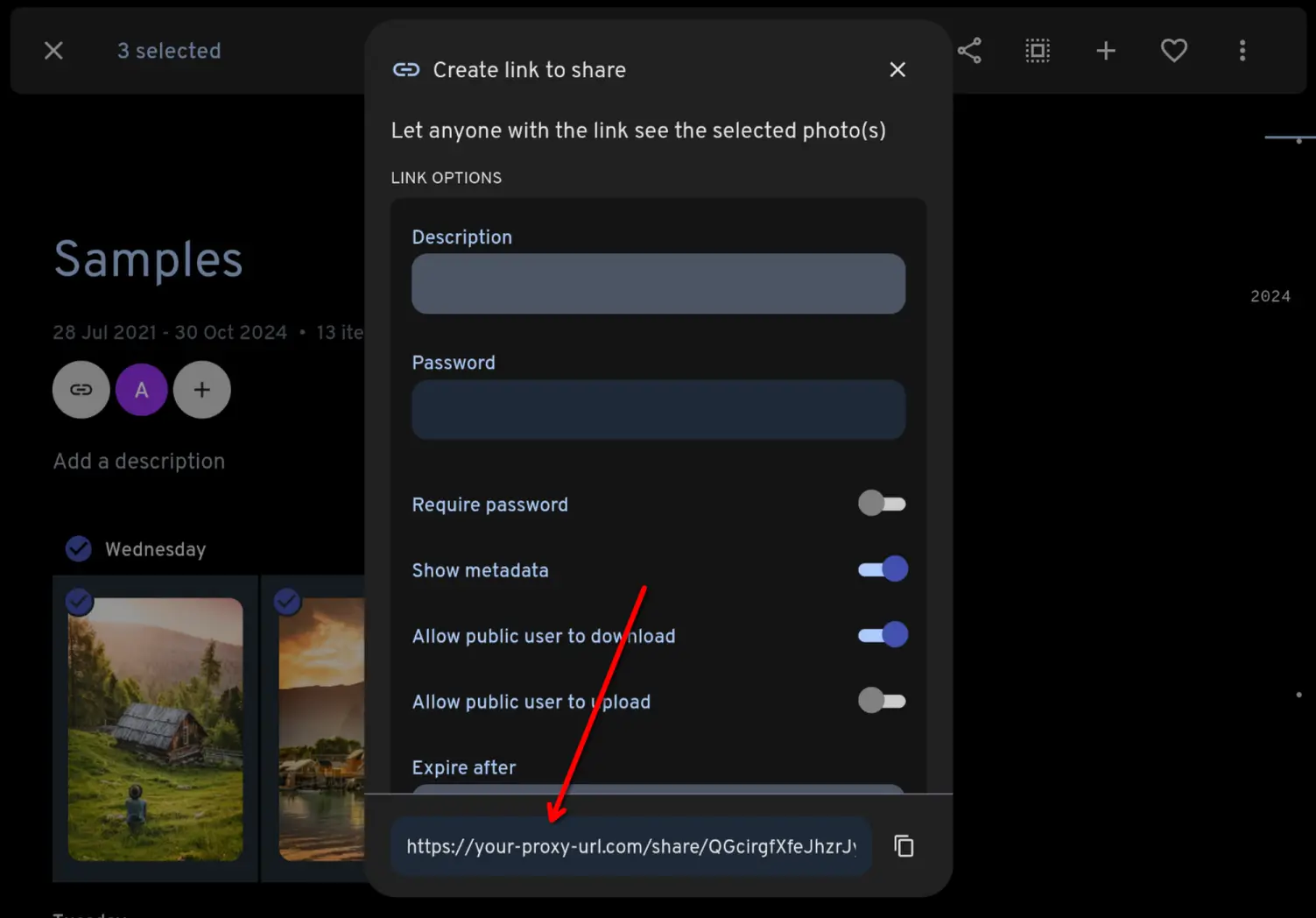
So I built a self-hosted app, Immich Public Proxy, which allows you to share individual files or full galleries to the public without ever exposing your Immich instance. This uses Immich's existing sharing functionality, so other than the initial configuration everything else is handled within Immich.
Why not just expose Immich publicly with Traefik / Caddy / etc?
To share from Immich, you need to allow public access to your /api/ path, which opens you up to potential vulnerabilities. It's up to you whether you are comfortable with that in your threat model.
This proxy provides a barrier of security between the public and Immich. It doesn’t forward traffic to Immich, it validates incoming requests and responds only to valid requests without needing privileged access to Immich.
Demo
You can see a live demo here, which is serving a gallery straight out of my own Immich instance.
Features
- Supports sharing photos and videos.
- Supports password-protected shares.
- Creating and managing shares happens through Immich as normal, so there's no change to your workflow.
Install
Setup takes about 30 seconds:
-
Take a copy of the docker-compose.yml file and change the address for your Immich instance.
-
Start the container: docker-compose up -d
-
Set the "External domain" in your Immich Server Settings to be whatever domain you use to publicly serve Immich Public Proxy. Now whenever you share an image or gallery through Immich, it will automatically create the correct public path for you.
For more detail on the steps, see the docs on Github.
It's all about the risk matrix. The theoretical likelihood of a vulnerability in Immich might be low, but the severity of that risk is catastrophic in terms of personal data leaking.
The likelihood of a risk in this proxy might be medium or even high according to you, but the severity is low. It doesn't have access to any of your personal data. All it does is talk to Immich via Immich's public sharing API.
One of the contributors to this project is bo0tzz, who is one of the maintainers of Immich.