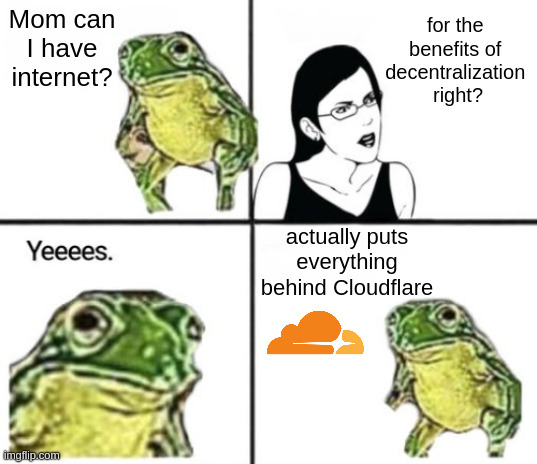
Though I'm not a big fan of centralization, I use cloudflare. Their DDoS protection is unmatched, they have scraping protection, and just in case they decide to screw their users over, switching to another service is trivial.
memes
Community rules
1. Be civil
No trolling, bigotry or other insulting / annoying behaviour
2. No politics
This is non-politics community. For political memes please go to !politicalmemes@lemmy.world
3. No recent reposts
Check for reposts when posting a meme, you can only repost after 1 month
4. No bots
No bots without the express approval of the mods or the admins
5. No Spam/Ads/AI Slop
No advertisements or spam. This is an instance rule and the only way to live. We also consider AI slop to be spam in this community and is subject to removal.
A collection of some classic Lemmy memes for your enjoyment
Sister communities
- !tenforward@lemmy.world : Star Trek memes, chat and shitposts
- !lemmyshitpost@lemmy.world : Lemmy Shitposts, anything and everything goes.
- !linuxmemes@lemmy.world : Linux themed memes
- !comicstrips@lemmy.world : for those who love comic stories.
I can stop drinking whenever I want.
If switching is trivial, why not do it now?
Their DDoS protection is unmatched
Is it? Try switching and see how often you are DDoSed.
I mean I don't really have a choice because i don't see a better way to put my home server on a url because I live in a dorm and can't port forward or get a static ip
cloudflare ddos protection is cetralization?
About 20% of global traffic is routed through Cloudflare so unfortunately Cloudflare is very much a massive case of centralization.
A Cloudflare outage would affect a huge number of websites and services and they have some degree of control over the way you host your and use their services.
Yeah, did people forget the last big Cloudflare outage already? A good chunk of all big services went down simultaneously. Discord, Amazon, Twitter and even the PS and Xbox consoles networks lmao.
How long before a website not behind something Cloudflare is considered suspicious or unwanted
Yes, use a competitor at least.
I deadass got a cloudflare error after reopening this post:

the people on selfhost would be very upset if they could read this.
if you can provide me a better way to keep my homelab from getting DDoSed every five minutes then by all means, please share it
Crowdsec+pangolin maybe? I would actually like to hear people's thoughts on this.
You don't need Cloudflare.
That doesn't help against a SYN flood.
From what I understand elsewhere in the thread, I believe that's just a matter of router configuration.
@DaPorkchop_@lemmy.ml @memes@lemmy.world Is that an actual issue or a hypothetical one? I've never had an attack in 10 years of publicly hosting stuff.
As someone else who used to host via an open port, you get random connections all the time. Almost constantly and the request paths make it obvious they are scanning for vulnerabilities. Via cloud flare the number of those requests is much lower, as they have to know at least the DNS to do so, (and can't guess it from a presented SSL cert.)
Yeah, I see random https and other connections all the time blindly scanning for vulnerabilities. Not enough to cause any real problems though. One time I publicly exposed redis or rabbitmq (can't remember which) and didn't set a password, so someone set a password for me :). That's about the worst that's happened to me.
It's the reason I set up cloudflare in the first place, so yeah. I was getting SYN flood-ed to the point that my router would just crash almost immediately, and after rebooting it the attack would resume after a minute or two.
Get a router that has flood protection? This is like.. Extremely basic network protection.
OpenWRT has had configurable syn-flood protection (enabled by default) since like 2010.
Even if the SYN packets were being ignored, the connection would still be unusable if there's enough incoming traffic for most legitimate packets to get dropped. And as mentioned in other comments, the router in question is a shitty ISP router which can't be replaced (although I do have a much fancier router with OpenWRT running behind that).
@DaPorkchop_@lemmy.ml @memes@lemmy.world Hm weird, I don't see why they would spend their resources attacking random people without any kind of demand. Even at work I've never seen one happening.
I still believe Cloudflare has most of its customers because of fearmongering tbh.
It's a bit like saying "having a password on your account is fearmongering, why would anyone try to access your data".
It's only fearmongering until you get attacked, and it's already too late when you do. Better to be proactive.
@Alaknar@sopuli.xyz @memes@lemmy.world Being proactive doesn't mean you have to hide your personal service behind a billion dollar company. That is precisely the kind of overreaction triggered by fearmongering. If you don't know how to secure access points or harden configurations, no service will be able to do it for you as if by magic. Not to mention your responsibility towards your users, who may not want to be tracked by a third-party company without their knowledge every time they visit your site (or half of the internet by now).
Is you homelab getting ddosed constantly?
I had had it for years and never ever got ddosed.
Are you sure it's actually ddos and not just the typical bots scanning for vulnerabilities? Which are easy defended for by keeping updated.
It's weird as a DDOS is not something that's just happens, it's a targeted attack. It's a rare occurrence that someone decided to attack a homelab.
I spent multiple days getting SYN flooded to the point my router would crash and reboot over and over, and it stopped the moment I set up cloudflare and asked my ISP to change my IP. This was the instance which pushed me over the edge, but there had been smaller attacks lasting a few minutes each for years leading up to this.
What kind of router to you have? A good router should not crash from any amount WAN traffic. But yes, if you host anything you will get scanned even harder than usual.
Just put it behind a wireguard server and don't expose any ports?
If you absolutely must expose some stuff, get a cheap 3$/mo vps that connects via wireguard to your home and setup a reverse proxy? They almost all come with DDoS protection.
How do I stop a DDOS attack of my website without having port 80 or 443 open, so you can access the website?
What's a good VPS provider for privacy enthusiasts?
I use Hetzner. Its fine. Boring/10 would use it again I guess?
Anubis:3
Could you shell out for a decent firewall? It should be able to protect against majority of ddos attacks unless someone is paying for something big.
But it really is fine to use cloudflare if you want the ddos protection. I wouldnt feel bad at all.
Don't forget your SSL certificate to prevent man-in-the-middle attacks. 🤪
Don't forget to have the SSL certificate supplied and managed by Cloudflare, of course 🤫
mTLS would solve your entire man in the middle problems.